Setup a VPN Connection into a PrivateLink ROSA Cluster with OpenVPN
This content is authored by Red Hat experts, but has not yet been tested on every supported configuration.
When you configure a Red Hat OpenShift on AWS (ROSA) cluster with a private link configuration, you will need connectivity to this private network in order to access your cluster. This guide will show you how to configute an AWS Client VPN connection so you won’t need to setup and configure Jump Boxes.
Prerequisites
- a private link ROSA Cluster - follow this guide to create a private ROSA Cluster
- jq
Set Envrionment Variables
Start by setting environment variables that we will use to setup the VPN connection
Create certificates to use for your VPN Connection
There are many ways and methods to create certificates for VPN, the guide below is one of the ways that works well. Note, that whatever method you use, make sure it supports “X509v3 Extended Key Usage”.
-
Clone OpenVPN/easy-rsa
-
Change to the easyrsa directory
-
Initialize the PKI
-
Edit certificate parameters
Uncomment and edit the copied template with your values
Uncomment (remove the #) the folowing field
-
Create the CA:
-
Generate the Server Certificate and Key
-
Generate Diffie-Hellman (DH) parameters
-
Generate client credentials
Import certficates into AWS Certificate Manager
-
Import the server certificate
- Before running the below commands, make sure you are still in the pki directory under the easyrsa3 directory
-
Import the client certificate
Create a Client VPN Endpoint
-
Retrieve the VPN Client ID
-
Associate each private subnet with the client VPN endpoint
-
Add an ingress authorization rule to a Client VPN endpoint
Configure your OpenVPN Client
-
Download the VPN Client Configuration
-
Run the following commands to add the certificates created in the first step to the VPN Configuration file.
- note: make sure you are still in the easy rsa / pki directory.
-
Add DNS Entries
In order to resolve the ROSA Cluster domain name, you will need to either add the DNS server and the Route 53 Hosted Domain for the cluster to your VPN settings or /etc/hosts in machine you are connecting from.
The DNS server will be the x.x.x.2 address of your VPC CIDR. For example, if you VPC CIDR is 10.66.0.0/16 then your DNS server will be 10.66.0.2
You can find the VPC ( machine ) CIDR with this command:
You can find the ROSA base domain with this command:
-
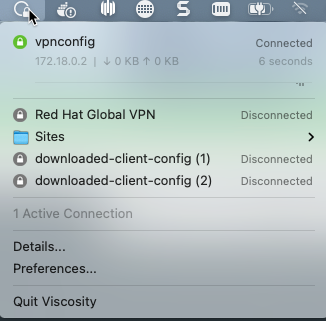
Import the client-config.ovpn file into your VPN Software.
-
Mac users - just double click the client-config.ovpn and it will be imported automatically into your VPN client.
-
Note: In order to connect to your cluster with the oc cli, you will need to update your OS DNS server with the DNS Server above after you connected to VPN.
-
-
Connect your VPN.