Cross-account Access using Custom OIDC Provider
This content is authored by Red Hat experts, but has not yet been tested on every supported configuration.
Access AWS Cross Account resources using OIDC
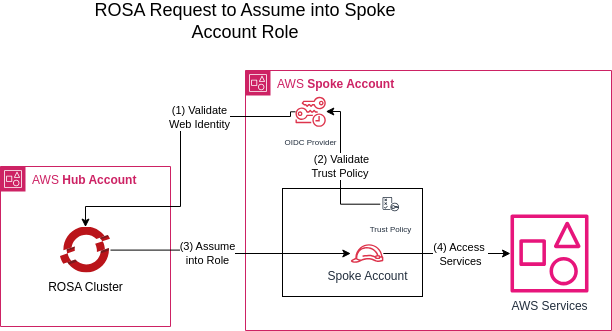
When employing ROSA, a common enterprise pattern involves establishing a cluster in a centralized AWS account while enabling development teams to manage services in their respective AWS accounts. This necessitates granting the ROSA cluster access to services residing in AWS accounts different from its own.
Various approaches exist to address this challenge, but one straightforward method is to establish a secondary OIDC provider in the AWS account of the development team, enabling direct access for pods.
Architecture
During the default STS ROSA Cluster creation, an “OpenID Connect Provider” is automatically generated in the same account as the cluster. This provider facilitates the ability of pods within our cluster to assume IAM Roles on the AWS Account using STS.
To enable pods to assume roles in other AWS accounts, we will essentially duplicate this OIDC Provider in the target account.
For clarity in this context, we will designate the AWS account housing our ROSA cluster as the Hub Account and the development team’s AWS account, containing the AWS resources we aim to access, as the Spoke Account.
Prerequisites
- A ROSA cluster deployed with STS - Hub Account
- Secondary AWS Account (no cluster required) - Spoke Account
- Accounts must have network access
- aws CLI
- oc CLI
- jq
Preparing Environment
-
Validate that your cluster has STS
You should see something like the following, if not you should not proceed, instead look to the Red Hat documentation on creating an STS cluster .
-
Create environment variables on Hub Account to refer to later
-
Create environment variables on Spoke Account to refer to later
This method may not work Cross Region
Create ODIC Provider on the Spoke Account
-
Obtain the ARN for the OpenID Connect associated with your Openshift Environment from the Hub Account
Find using command below:
-
Obtain the OIDC thumbprint from the OIDC Provider in the Hub Account
-
On the Spoke Account create a new OpenID Connect Provider file using the values obtained from the hub account
Make sure the
OIDC_ENDPOINTandOIDC_THUMBPRINTvariables have been transferred from the hub to spoke account + Tip: Can be done by copying the output fromenv | grep OIDC_command into your Spoke Account
Create Trust Policy between Provider and IAM Role
-
Create IAM Role trust policy document on the Spoke Account
-
Create IAM Role on Spoke Acocunt
Create Test Application
Verify our capability to assume the role established in our spoke account using the recently generated OIDC provider.
-
Login to Openshift on the Spoke Account
-
Create an OpenShift project
-
Annotate the default service account to use the STS Role
-
Create a Pod using a container that has access to the AWS CLI
-
Verify the Pod is using the correct AWS identity
Stretch Goal
Utilize the previously established custom OIDC provider to finalize the AWS Secrets Experts Article , where the SecretManager secret is stored in your Spoke Account.
Cleanup
-
Delete application
-
Delete AWS Roles and Policies on the Spoke Account
