Configure Microsoft Entra ID as an OIDC identity provider for ARO with cli
This content is authored by Red Hat experts, but has not yet been tested on every supported configuration.
The steps to add Azure AD as an identity provider for Azure Red Hat OpenShift (ARO) via cli are:
- Prerequisites
-
Azure
- Define needed variables
- Get oauthCallbackURL
-
Create
manifest.jsonfile to configure the Azure Active Directory application - Register/create app
- Add Service Principal for the new app
- Make Service Principal an Enterprise Application
- Create the client secret
- Update the Azure AD application scope permissions
- Get Tenant ID
- OpenShift
Prerequisites
Have Azure cli installed
Follow the Microsoft instuctions: https://docs.microsoft.com/en-us/cli/azure/install-azure-cli
Note
This has been written for az cli verion 2.37.0 some commands will not work with previous versions, however, there is a known issue
https://github.com/Azure/azure-cli/issues/23027
where we will use an older version via podman run -it mcr.microsoft.com/azure-cli:2.36.0 .
In case you’re using docker, just replace podman command by docker .
For podman installation on Mac, Windows & Linux, please refer to
https://podman.io/getting-started/installation
Login to Azure
Login to Azure as follows:
If you’re logging in from a system you have no access to your browser you can authenticate, you can also use
Azure
Define needed variables
To simplly follow along, first define the following variables according to your set-up:
Get oauthCallbackURL
To get the oauthCallbackURL for the Azure AD integration, run the following commands:
Note
oauthCallbackURL, in particular AAD can be changed but must match the name in the oauth providerwhen creating the OpenShift OpenID authentication
Create manifest.json file to configure the Azure Active Directory application
Configure OpenShift to use the email claim and fall back to upn to set the Preferred Username by adding the upn as part of the ID token returned by Azure Active Directory.
Create a manifest.json file to configure the Azure Active Directory application.
Register/create app
Create an Azure AD application and retrieve app id:
Add Service Principal for the new app
Create Service Principal for the app created:
Make Service Principal an Enterprise Application
We need this Service Principal to be an Enterprise Application to be able to add users and groups, so we add the needed tag (az cli >= 2.38.0)
Note
In case you get a trace back (az cli = 2.37.0) check out
https://github.com/Azure/azure-cli/issues/23027
To overcome that issue, we’ll do the following
Create the client secret
The password for the app created is retrieved by resetting the same:
Note
The password generated with above command is by default valid for one year and you may want to change that by adding either and end date via
--end-date or set validity in years with --years.
For details consult the
documentation
Update the Azure AD application scope permissions
To be able to read the user information from Azure Active Directory, we need to add the following Azure Active Directory Graph permissions
Add permission for the Azure Active Directory as follows:
- read email
- read profile
- User.Read
Note If you see a message that you need to grant consent you can safely ignore it, unless you are authenticated as a alobal administrator for this Azure Active Directory. Standard domain users will be asked to grant consent when they first login to the cluster using their AAD credentials.
Get Tenant ID
We do need the Tenant ID for setting up the Oauth provider later on:
Note
Now we can switch over to our OpenShift installation and apply the needed configuraion.
Please refer to
https://docs.openshift.com/container-platform/latest/cli_reference/openshift_cli/getting-started-cli.html
to get the latest oc cli
OpenShift
Login to OpenShift as kubeadmin
Fetch kubeadmin password and login to your cluster via oc cli (you can use any other cluster-admin user in case you have already created/added other oauth providers)
Create an OpenShift secret###
Create an OpenShift secret to store the Azure Active Directory application secret from the application password we created/reset earlier:
Apply OpenShift OpenID authentication
As a last step we need to apply the OpenShift OpenID authentication for Azure Active Directory:
Wait for authentication operator to roll out
Before we move over to the OpenShift login, let’s wait for the new version of the authentication cluster operator to be rolled out
Note it may take some time until the rollout starts
Verify login through Azure Active Directory
Get console url to login:
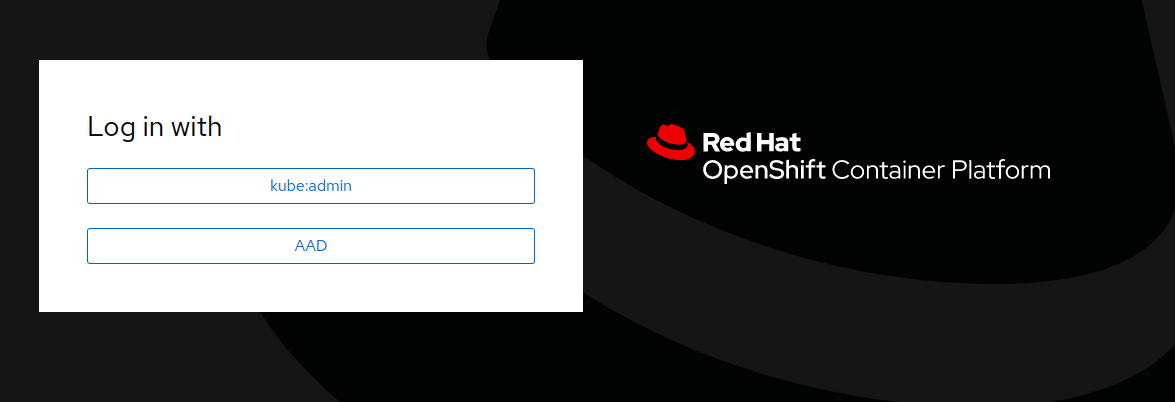
Opening the url in a browser, we can see the login to Azure AD is available
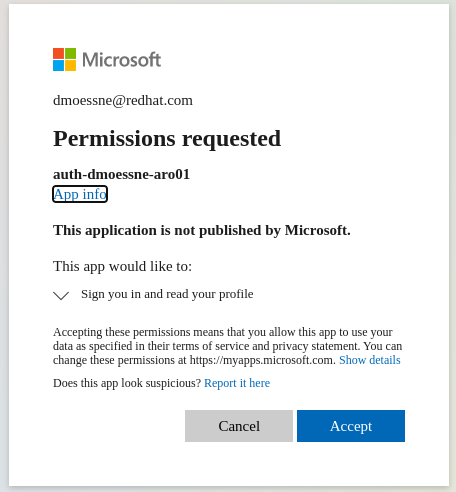
At first login you may have to accept application permissions
Last steps
As a last step you may want to grant a user or group cluster-admin permissions and remove kubeadmin user, see
