Private ARO Cluster with access via JumpHost
This content is authored by Red Hat experts, but has not yet been tested on every supported configuration.
A Quickstart guide to deploying a Private Azure Red Hat OpenShift cluster.
Authors: Paul Czarkowski , Ricardo Macedo Martins
Prerequisites
Azure CLI
Obviously you’ll need to have an Azure account to configure the CLI against.
MacOS
See Azure Docs for alternative install options.
-
Install Azure CLI using homebrew
-
Install sshuttle using homebrew
Linux
See Azure Docs for alternative install options.
-
Import the Microsoft Keys
-
Add the Microsoft Yum Repository
-
Install Azure CLI
Prepare Azure Account for Azure OpenShift
-
Log into the Azure CLI by running the following and then authorizing through your Web Browser
-
Make sure you have enough Quota (change the location if you’re not using
East US)see Addendum - Adding Quota to ARO account if you have less than
36Quota left forTotal Regional vCPUs. -
Register resource providers
Get Red Hat pull secret
-
Log into cloud.redhat.com
-
Browse to https://cloud.redhat.com/openshift/install/azure/aro-provisioned
-
click the Download pull secret button and remember where you saved it, you’ll reference it later.
Deploy Azure OpenShift
Variables and Resource Group
Set some environment variables to use later, and create an Azure Resource Group.
-
Set the following environment variables
Change the values to suit your environment, but these defaults should work. -
Create an Azure resource group
-
Create an Azure Service Principal
Networking
Create a virtual network with two empty subnets
-
Create virtual network
-
Create control plane subnet
-
Create machine subnet
-
Disable network policies for Private Link Service on the control plane subnet
Optional. The ARO RP will disable this for you if you skip this step.
Egress
Public and Private clusters will have –outbound-type defined to LoadBalancer by default. It means all clusters by default have open egress to the internet through the public load balancer.
To change the default behavior and restrict the Internet Egress you have to set --outbound-type to UserDefinedRouting during cluster creation, and set up a traffic to run through a Firewall solution. This can either be a 3rd party solution or a native Azure solution such as Azure Firewall/Azure NAT Gateway.
If you want to proceed with the UserDefinedRouting the two examples below show how this can be achieved through either Azure NAT gateway or Azure Firewall + Internet Egress.
1a. NAT Gateway
This option replaces the routes for the cluster to go through the Azure NAT GW service for egress vs the LoadBalancer. This will incur extra Azure costs.
-
Create a Public IP
-
Create the NAT Gateway
-
Get the Public IP of the NAT Gateway
-
Reconfigure Subnets to use Nat GW
1b. Firewall + Internet Egress
This option replaces the routes for the cluster to go through Azure Firewall for egress traffic, rather than the LoadBalancer. This will incur extra Azure costs.
-
Make sure you have the AZ CLI firewall extensions
-
Create a firewall network, IP, and firewall
-
Configure the firewall and configure IP Config (this may take 15 minutes)
-
Create and configure a route table
-
Create firewall rules for ARO resources
Note: ARO clusters do not need access to the internet, however your own workloads running on them may. You can skip this step if you don’t need any egress at all. -
Create a Network Rule to allow all http/https egress traffic (not recommended)
-
Create Application Rules to allow to a restricted set of destinations
replace the target-fqdns with your desired destinations
-
-
Update the subnets to use the Firewall
Once the cluster is deployed successfully you can update the subnets to use the firewall instead of the default outbound loadbalancer rule.
Create the cluster
This will take between 30 and 45 minutes.
--outbound-type UserDefinedRouting flag if you are not using the default routing.Jump Host
With the cluster in a private network, we can create a Jump host in order to connect to it. You can do this while the cluster is being created.
-
Create jump subnet
-
Create a jump host
-
Save the jump host public IP address
-
Use sshuttle to create a ssh vpn via the jump host (use a separate terminal session)
replace the IP with the IP of the jump box from the previous step. -
Get OpenShift console URL
set these variables to match the ones you set at the start. -
Get OpenShift credentials
-
log into OpenShift
Delete Cluster
Once you’re done its a good idea to delete the cluster to ensure that you don’t get a surprise bill.
-
Delete the cluster
-
Delete the Azure resource group
Only do this if there’s nothing else in the resource group.
Addendum
Adding Quota to ARO account
-
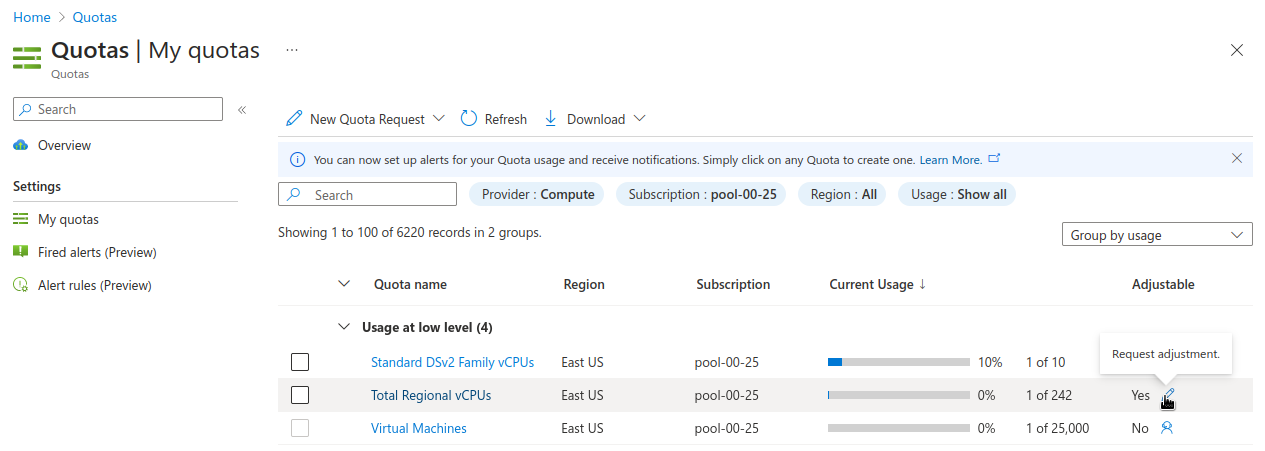
Choose the appropriate filters:
-
Set Provider to “Compute”
-
Set Subscription to the subscription you are creating the cluster in
-
Set Region to “East US” and uncheck the other region boxes
-
-
Search for the quota name that you want to increase. This may be “Total Regional vCPUs” if you checked that prior to creating the cluster, or it may be a specific resource quota named in a
ResourceQuotaExceedederror message. Note that in the latter case, the Azure console uses a localized display name (for exampleStandard DSv3 Family vCPUsrather than an identifier namestandardDSv3Familymentioned in the error message. -
Next to the quota name you wish to increase, click the pencil in the Adjustable column to request adjustment
-
Enter the new desired quota in the New limit text box. By default, a cluster will need 36 additional Regional vCPUs beyond current usage, or the
ResourceQuotaExceedederror message will tell you how much more of an additional resource is needed. -
Click Submit. You may need to go through additional authentication.
-
Azure will review your request to adjust your quota. This may take several minutes.
